- cross-posted to:
- security@lemmy.ml
- cross-posted to:
- security@lemmy.ml
They noticed that some ssh sessions took 0.5 seconds too long under certain circumstances. 😲
Holy hell that’s good QA.
Microsoft employee.
Definitely not from the team working on search on Windows then.
Don’t see why you’re being downvoted, the person in question who discovered this is a postgres maintainer employed by Microsoft.
Probably people think this is a troll or something.
I wrote it because I was surprised, especially since I’m not a fan of microsoft and their policies. Lately, I have the feeling Microsoft is better than Google (relative terms) when it comes to oss.
What is additionally surprising is the breaches of Microsoft services in the last year. There is one every few weeks or so… And then they pick up a backdoor because login took 0.5 instead of 0.1s.
Anyway, his findings are amazing.
This isn’t the same thing, but I’m reminded of Minecraft.
Minecraft is a massively popular game. Notch once said he planned to make it open source when its popularity died down. But now Microsoft owns it.
Not only that, but Mojang accounts don’t work anymore. You have to have a Microsoft account to play it now. Even trying to download and play an older version of the game offline requires Microsoft to approve it. Microsoft is actively tightening the leash on the game because it makes them money. Open sourcing the game will likely never happen now. The best we can hope for it for versions to fall into public domain after 70-ish years.
That’s how I see Microsoft. They only care about what its beneficial for them to drive profits. Working on open source projects, and open sourcing a few of their tools to get the benefits of community adoption and code review is great, sure. But they’d sooner try to incorporate Linux into Windows to keep people in their surveillance ecosystem, than to open source Windows.
Remember when Windows 10 was the last version, until they changed their minds? Remember when they floated the idea of charging a recurring subscription to use Windows, before they silently dropped the idea? Remember when there was credible talk about the next version of Windows being cloud-based where they controlled all your data and you had no privacy? Hell, you have basically no privacy on Windows 10. Trying to reclaim some involves registry edits, special third party tools, and a constant battle with automatic updates reverting your changes.
I’ll say it again. Microsoft doesn’t care about OSS. It’s just currently beneficial for them to pretend they do.
Goggle seemed to care a lot about OSS, then started making everything in Android depend on their proprietary ecosystem to function. Now Google is using the dominant position they got by taking advantage of OSS adoption, and have been pushing privacy-invading standards and trying to get rid of ad blockers online, among many other things.
For these huge companies, OSS is just a tool to get more control and power. The moment it’s no longer useful, they’ll find ways to work around the license and enshitify everything again.
It keeps happening. I refuse to keep trusting bad actors every time they dangle a shiny trinket over our heads.
I do appreciate the work this person did in finding the bug. It’s not all doom and gloom.
I agree with you sentiment here. That’s why I wrote ‘relative terms’ in my comment.
Since Nadela took over, Microsoft did some open thing which benefited community. So, Microsoft opened somewhat.
During the same time, under Pichai, google went the other way: they focus more on monetization and try to control stuff the apple way. Manifest v3? Google also didn’t do anything really worth mentioning in the last 10y in terms of products. Well, except ‘attention’ article. And even this they didn’t believe in and they cannot deliver a decent product. I just tried google advanced Gemini and it’s, to put it politely, shit. Google also had some positive actions like mainlining a lot of stuff in Linux Kernel to more easily upgrade android.
So, while google is closing down and making mistakes, Microsoft is opening a bit up.
If you look the state from the last year and the state now. Microsoft improved. Google went the other way.
Microsoft doesn’t care about open source, they care about the money Cloud Services using open source bring them. I don’t think google cares as well. For reason read this: https://www.joelonsoftware.com/2002/06/12/strategy-letter-v/
Well half a second delay is pretty noticeable when you ssh into a machine sitting right next to you. It should be instant. And if it isn’t something’s off.
Damn, it is actually scary that they managed to pull this off. The backdoor came from the second-largest contributor to xz too, not some random drive-by.
Time to audit all their contributions although it looks like they mostly contribute to xz. I guess we’ll have to wait for comments from the rest of the team or if the whole org needs to be considered comprimised.
deleted by creator
This is a fun one we’re gonna be hearing about for a while…
It’s fortunate it was discovered before any major releases of non-rolling-release distros were cut, but damn.
The person who found the backdoor : https://mastodon.social/@AndresFreundTec/112180083704606941
Time to bring back the reproducible build hype
Won’t help here; this backdoor is entirely reproducible. That’s one of the scary parts.
The backdoor wasn’t in the source code, only in the distributed binary. So reproducible builds would have flagged the tar as not coming from what was in Git
Reproducible builds generally work from the published source tarballs, as those tend to be easier to mirror and archive than a Git repository is. The GPG-signed source tarball includes all of the code to build the exploit.
The Git repository does not include the code to build the backdoor (though it does include the actual backdoor itself, the binary “test file”, it’s simply disused).
Verifying that the tarball and Git repository match would be neat, but is not a focus of any existing reproducible build project that I know of. It probably should be, but quite a number of projects have legitimate differences in their tarballs, often pre-compiling things like autotools-based configure scripts and man pages so that you can have a relaxed
./configure && make && make installbuild without having to hunt down all of the necessary generators.Time to change that tarball thing. Git repos come with built in checksums, that should be the way to go.
The back door is not in the source code though, so it’s not reproducible from source.
Part of the payload was in the tarball. There was still a malicious shim in the upstream repo
Why didn’t this become a thing? Surely in 2024, we should be able to build packages from source and sign releases with a private key.
It’s becoming more of a thing but a lot of projects are so old that they haven’t been able to fix their entire build process yet
Probally more SLSA which reproducible builds is apart of
Reading the comments here https://news.ycombinator.com/item?id=39865810 it appears that libarchive may be tainted as well.
Lzma balls
Here is the official statement from OpenSUSE: https://news.opensuse.org/2024/03/29/xz-backdoor/
t y for sharing.
#showerthoughts The problem is in upstream and has only entered Debian Sid/unstable. Does this mean that for example bleeding edge Arch (btw) sshd users are compromised already ?
Arch is on 5.6.1 as of now: https://archlinux.org/packages/core/x86_64/xz/
We at Nixpkgs have barely evaded having it go to a channel used by users and we don’t seem to be affected by the backdoor.
Arch had a patch rolled out yesterday [1][2][3] that switches to the git repo. On top of that the logic in the runtime shim and build script modifier was orchestrated to target Debian and RPM build systems and environments [4].
[2] https://gitlab.archlinux.org/archlinux/packaging/packages/xz/-/issues/2
[3] https://security.archlinux.org/CVE-2024-3094
[4] https://www.openwall.com/lists/oss-security/2024/03/29/4
Homebrew rolled back the release after finding out
Here’s a link to the PR for anyone who’s interested
Damn fine work all around.
I know this is an issue fraught with potential legal and political BS, and it’s impossible to check everything without automation these days, but is there an organization that trains and pays people to work as security researchers or QA for open source projects?
Basically, a watchdog group that finds exploitable security vulnerabilities, and works with individuals or vendors to patch them? Maybe make it a publicly owned and operated group with mandatory reporting of some kind. An international project funded by multiple governments, where it’s harder for a single point of influence to hide exploits, abuse secrets, or interfere with the researchers? They don’t own or control any code, just find security issues and advise.
I don’t know.
Just thinking that modern security is getting pretty complicated, with so many moving parts and all.
It seems like a RCE, rather an auth bypass once though. https://bsky.app/profile/filippo.abyssdomain.expert/post/3kowjkx2njy2b
could a Flatpak contain one of the backdoored builds of
xzorliblzma? Is there a way to check? Would such a thing be exploitable, or does this backdoor only affect ssh servers?The base runtime pretty much every Flatpak uses includes xz/liblzma, but none of the affected versions are included. You can poke around in a base runtime shell with
flatpak run --command=sh org.freedesktop.Platform//23.08or similar, and check your installed runtimes withflatpak list --runtime.23.08 is the current latest version used by most apps on Flathub and includes xz 5.4.6. 22.08 is an older version you might also still have installed and includes xz 5.2.12. They’re both pre-backdoor.
It seems there’s an issue open on the freedesktop-sdk repo to revert xz to an even earlier version predating the backdoorer’s significant involvement in xz, which some other distros are also doing out of an abundance of caution.
So, as far as we know: nothing uses the backdoored version, even if it did use that version it wouldn’t be compiled in (since org.freedesktop.Platform isn’t built using Deb or RPM packaging and that’s one of the conditions), even if it was compiled in it would to our current knowledge only affect sshd, the runtime doesn’t include an sshd at all, and they’re still being extra cautious anyway.
One caveat: There is an unstable version of the runtime that does have the backdoored version, but that’s not used anywhere (I don’t believe it’s allowed on Flathub since it entirely defeats the point of it).
Some no-name came and without any problems asked to become a maintainer in a project used in almost any distro, took it over, put a backdoor in there and no one had any questions? In this case, everything turned out thanks to pure chance. Noname screwed up his backdoor, which attracted the attention of a guy from Microsoft, and out of boredom, he dug up what was what. And if I hadn’t messed up, or that guy from Microsoft decided to go drink beer instead of poking around in the xz code, then no one would have discovered anything. It’s scary to imagine how many of these nonames are sitting in all these thousands of open source projects, waiting in the wings to roll out a malicious patch.
Since the actual operation of the liblzma SSH backdoor payload is still unknown, there’s a protocol for securing your impacted systems:
• Consider all data, including key material and secrets on the impacted system as compromised. Expand the impact to other systems, as needed (for example: if a local SSH key is used to access a remote system then the remote system must be considered impacted as well, within the scope the key provides).
• Wipe the impacted host and reinstall it from scratch. Use known good install that does not contain the malicious payload. Generate new keys and passwords. Do not reuse any from the impacted systems.
• Restore configuration and data from backups, but from before the time the malicious liblzma package was installed. However, be careful not to allow potentially leaked credentials or keys to have access to the newly installed system (for example via $HOME/.ssh/authorized_keys).
This handles the systems themselves. Unfortunately any passwords and other credentials stored, accessed or processed with the impacted systems must be considered compromised as well. Change passwords on web sites and other services as needed. Consider the fact that the attacker may have accessed the services and added ways to restore access via for example email address or phone number in their control. Check all information stored on the services for correctness.
This is a lot of work, certainly much more than just upgrading the liblzma package. This is the price you have to pay to stay safe. Just upgrading your liblzma package and hoping for the best is always an option, too. It’s up to you to decide if this is a risk worth taking.
This recovery protocol might change somewhat once the actual operation of the payload is figured out. There might be situations where the impact could be more limited.
As an example: If it turns out that the payload is fully contained and only allows unauthorized remote access via the tampered sshd, and the host is not directly accessible from the internet (the SSH port is not open to internet) this would mean that it might be possible to clean up the system locally without full reinstall.
However, do note that the information stored on the system might have still been leaked to outside world. For example leaked ssh keys without a passphrase could still afford the attacker access to remote systems.
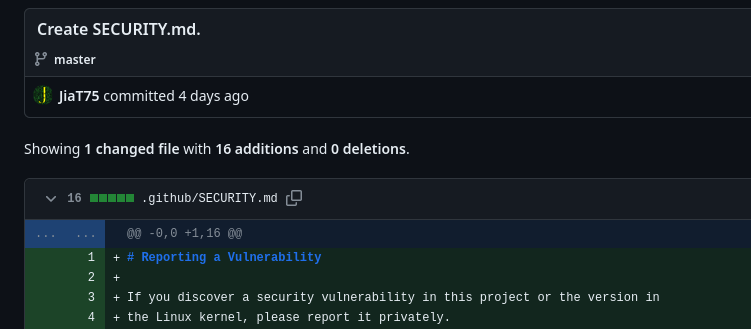
This is a long con, and honestly the only people at fault are the bad actors themselves. Assuming Jia Tan’s GitHub identity and pgp key weren’t compromised by someone else, this backdoor appears to be the culmination of three years of work.