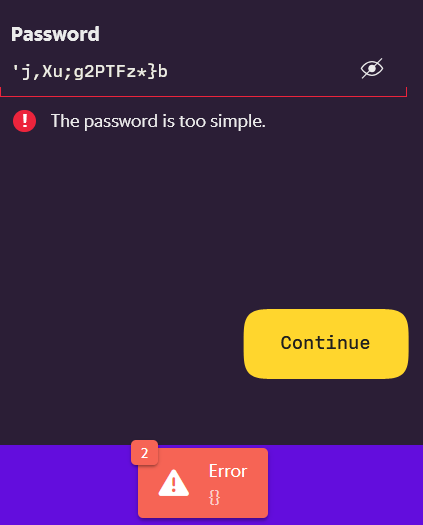
“Your selected password is already being used by SwiftyFan05. Please choose another password.”
another_password
Somebody isn’t sanitizing their inputs properly. Like putting a bandaid on a heart attack
Which is ridiculous because it’s going to hash down to the same character set. There’s no way they’re storing your password with special characters unhashed, right?
One can hope 🤞
Lol I recently have found the opposite!
Fandom is gross anyway. Contributing to independent wikis is a much better use of your time. https://getindie.wiki/
It’s not Fandom
they don’t specify a limit so 64 character password it is.
Go all in, 1024 character password.
Bcrypt/Scrypt have a 72 byte limit. Developers can get around that by putting it through a regular hash first, but that’s not common.
My previous bank forced 8 characters with only numbers and letters.
Hunter2
I don’t get it, why did you type all asterisks‽
What’s not to get? He made his password 7 asterisks. Funny, because it’s the same as mine.
We are all hunter2 on this blessed day.
64 characters picked at random in
[a-zA-Z0-9_]is perfectly fine if password is your only option. Special character do not increase significantly the difficulty of bruteforcing it, but introduce the risk of having to manually type"}à.å÷Â!!ç-×ô@¸Á¢±ãÕß>>úÓ}¼º¤«<_`àÅû§Æ]*ÂñçÌÿ§à®&ܱ=Ú-´ð¹é$.>=;Öif something goes catastrophically wrong.It’s actually nice they have underscore. 😀
Yes because if you choose 8 characters at random, with 25 small + 25 big letters and 10 numeric, it* only 60^8 = 167,961,600,000,000 combinations.
I think the problem is more if the system allows brute force with thousands of erroneous attempts.
Then statistically any hacker can attempt several accounts, and ultimately get lucky. But by all means, put the responsibility to the user, users are the experts right!?
I never got the frantic excessive entropy mindset, when the problem is much simpler to not allow crackers endless attempts. You can allow 50 attempts, and chances would be very slim to guess even pretty moronic passwords.What’s even worse is when they REQUIRE big and small and numbers to maximize entropy, they actually make statistically FEWER attempts necessary to brute force it.
A standard Microsoft introduced in the 90’s, and FUCKING almost everybody is using, despite it’s a 100% moronic requirement.
Instead just warn against passwords that can be guessed by logic, or can be found in a dictionary.Most websites don’t allow multiple failed logins and, even if they did, the network latency alone would make brute force attacks useless. The point of having a high entropy password is to protect against hackers brute forcing a leaked database of hashes. Having different passwords for every website also protects against this so, as usual, the answer is “just use a password manager”.
just use a password manager
I will never do that, I have a system instead. I never understood why people would want to use a password manager. To me it seems it ads an attack vector, where you could lose EVERYTHING!
I guarantee your system is less secure than the worst password manager. Humans are inherently bad at choosing passwords, or anything to do with randomness really.
That is true for online password managers, you need an offline one
Passwords suck as an authentication system in general. Your own system is probably worse than what password managers do. Yes, there are problems, but so does every other solution to this, and password managers win out in the comparison.
Your own system is probably worse than what password managers do.
How so? If you use a password manager across 3 platforms, that makes for 3 attack vectors.
My personal system has guaranteed no vulnerabilities. So how do you conclude my system is worse?My personal system has guaranteed no vulnerabilities
If you think that’s true, then you don’t have the experience to make a secure system.
What? What kind of system do you think I have? The only vulnerability is if they can hack my brain.
Yeah, that’s going to be a terrible system. The human brain isn’t capable of keeping track of enough entropy to create a secure password system.
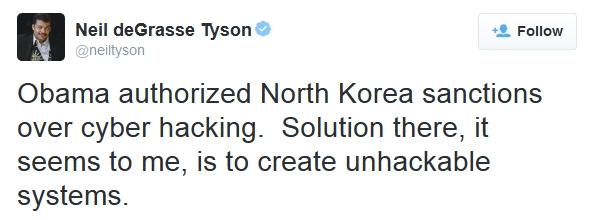
More generally, it’s a big red flag when anybody thinks they can make a better system than publicly available and verified systems. You’re not capable of that, I’m not capable of that, Bruce Schneier is not capable of that. No matter how smart you are, you missed something. That’s why I didn’t need to know a single detail.
The point of having a high entropy password is to protect against hackers brute forcing a leaked database of hashes.
Seems a bit stupid if a database of passwords or other sensitive information can be brute forced.
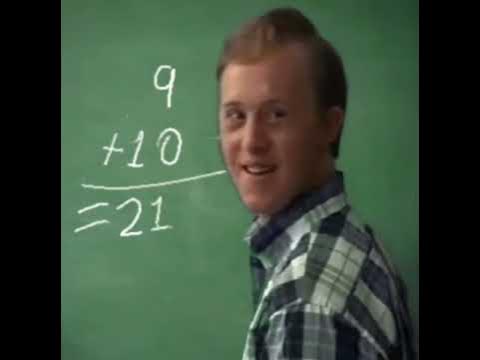
Please clarify what you mean because your comment is giving me these vibes.
what’s an example of password that can be guessed by logic?
Something that can possibly be deduced knowing personal information, like a birth date.
recently did one that only cared about being very long, so i typed thispasswordisfuckinglong and it took it
Try this one, has lots of special characters:
a_a_a_a_a_a_a_aThis one too: _____________
or the entirety of the Bible with special characters removed and spaces replaced with underscores
I mean, 63^6 is a lot of possibilities, but just make the password longer to increase its security.
Blocking out special characters is dumb, but as others have pointed out, they’re probably not sanitizing inputs.
You might want to try out: https://libraryofbabel.info/random.cgi
I hate these arbitrary limitations of 16 characters, 25 is unbreakable and some sites won’t allow longer than 16 20, I’ve even had one site not allow over 6.
Ah, I’ve done that before, 1/100 odds it’s because someone doesn’t want to fuck with RegEx.
It says NO special characters!