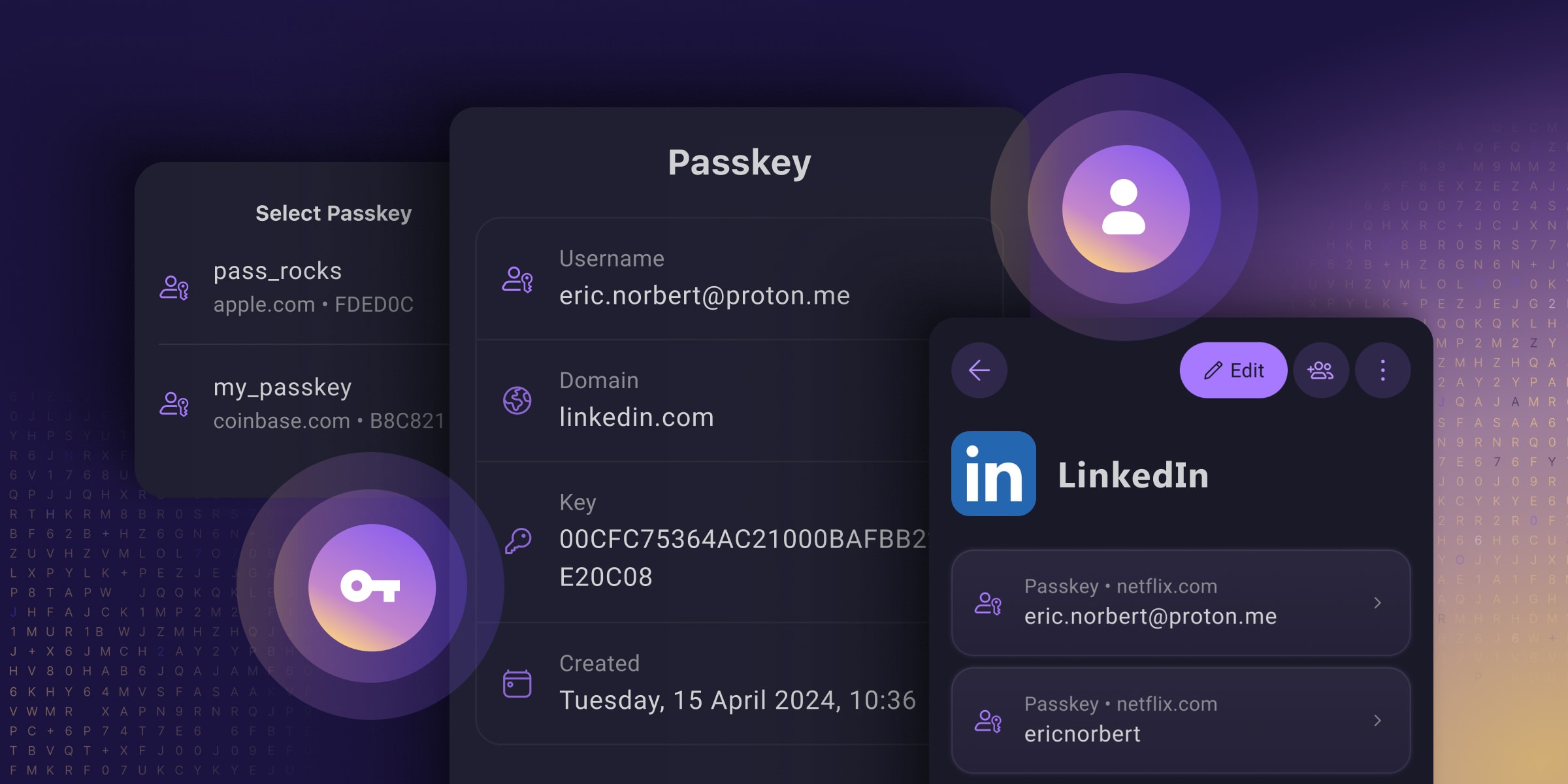
Passkeys are an easy and secure alternative to traditional passwords that can help prevent phishing attacks and make your online experience smoother and safer.
Unfortunately, Big Tech’s rollout of this technology prioritized using passkeys to lock people into their walled gardens over providing universal security for everyone (you have to use their platform, which often does not work across all platforms). And many password managers only support passkeys on specific platforms or provide them with paid plans, meaning you only get to reap passkeys’ security benefits if you can afford them.
They’ve reimagined passkeys, helping them reach their full potential as free, universal, and open-source tech. They have made online privacy and security accessible to everyone, regardless of what device you use or your ability to pay.
I’m still a paying customer of Bitwarden as Proton Pass was up to now still not doing everything, but this may make me re-evaluate using Proton Pass as I’m also a paying customer of Proton Pass. It certainly looks like Proton Pass is advancing at quite a pace, and Proton has already built up a good reputation for private e-mail and an excellent VPN client.
Proton is also the ONLY passkey provider that I’ve seen allowing you to store, share, and export passkeys just like you can with passwords!
See https://proton.me/blog/proton-pass-passkeys
#technology #passkeys #security #ProtonPass #opensource
Proton is also the ONLY passkey provider that I’ve seen allowing you to store, share, and export passkeys just like you can with passwords!
1Password has had this for several months.
As others have mentioned, Bitwarden also has this. This really feels like an ad.
Agreed. Saying PP four times in two sentences triggers my ad sense. Capitalism never capitulates.
i looked at it and it literally says passkeys aren’t supported on Android right now. so this is bullshit.
Looks like they are just rolling out support for Android 14 and up.
sry my comment was not clear i meant proton.
Thanks I did not know that. I see they say share via the vault, but don’t specifically mention exporting, as in to a file for importing elsewhere outside 1Password. But certainly LastPass, Bitwarden and others I’d looked at were not exporting the passkeys.
Bitwarden only works on the desktop with a browser extension. So as much as I have Passkeys in Bitwarden they are not usable on my phone :(
Doesn’t Bitwarden already have that feature? https://bitwarden.com/passwordless-passkeys/
Bitwarden currently only supports storing and using Passkeys via the browser extension. You cannot use them on mobile.
Ah I see. Hope to see it brought to mobile soon.
They’re rewriting their mobile apps to make it possible
But the Bitwarden extension works on Android Firefox, so you could probably use it that way.
Seems that way? Although I can’t seem to create a passkey somehow. Or is that how it works? Should I be able to create one on a free Bitwarden plan?
Edit: only on browser extension, got it.
Yes, but as I said, as of yesterday still not implemented on mobile.
I don’t think it has the ability to export/share.
Like in a file?
Bitwarden already syncs between PC and phone.
By “Share”, I assumed with other password managers that supported PassKeys.
It doesn’t necessarily have to be a file, it could be the config like a TOTP code is.
When you say bitwarden syncs between PC and phone, which service does it sync with on these platforms? I didn’t know bitwarden synced with any other service.
They will have to rip Bitwarden (soon Vaultwarden) from my cold dead hands.
When are they changing their name? I didn’t even know
They aren’t. Vaultwarden is the selfhosted version.
True, it is good, but they need to speed up on passkeys for mobile as many do use mobile devices and what’s the point of having passkeys on desktop.
I have a question that is kind of off topic. If I use a password manager and generally use randomized secure passwords, do passkeys offer any additional security?
By practicing good password behavior, I have struggled to see how the benefits of passkeys out weigh the hassles.
Yes, passkeys are not brute-forcible, and are phishing resistant.
Whether or not they provide more security depends on how fully they’re implemented. A service that’s fully implemented them, like PlayStation for example, will remove the password from your account after activating your passkey.
Some websites have half-assed their implementations where you can use a passkey or a password to log in. In that scenario, your account isn’t really any more secure, it’s just a more convenient way to log in.
Are sufficiently long passwords susceptible to brute force attacks?
Don’t passkeys get that feature by just being longer?
Are sufficiently long passwords susceptible to brute force attacks?
Yes. Thought obviously the odds of success go down the longer and more complex that password.
Don’t passkeys get that feature by just being longer?
Put simply… no. Passkeys aren’t just ”longer passwords” sent to the same place. Unlike passwords, Passkeys aren’t a “shared secret” that you’re sending to the service you’re authenticating to. Passkeys use asymmetric encryption and are neither sent to nor stored on the server you’re authenticating to. Your passkey is a private key stored on your device and secured by biometrics, the paired public key for which lives on the server you created the passkey to authenticate to.
In a traditional brute force operation, you’re sending guesses to a server that knows your password. If you send the correct guess, you get in. It’s also possible to steal the password from the server and brute force that offline.
With a passkey on the other hand, the server uses your public key to encrypt a string in a challenge message, this string can only be decrypted by your passkey. You then send a response that’s encrypted by your private key, which can then only be decrypted by the public key on the server. So the thing you’re sending to the server to authenticate isn’t your passkey, and it’s unique every time you log in.
So could you perform some kind of operation that would technically still be a kind of brute force? Theoretically yeah. But even so you’d be limited to brute forcing against the server, which isn’t very effective even against passwords. However you would not at all be susceptible to offline brute forcing based on the capture of a passkey either in flight by breaking encryption, or by breaching the server, because your passkey never leaves your device.
Thank you, that was a really helpful explanation that I haven’t seen elsewhere. It helps a lot and I think I now understand the difference between passwords and passkeys.
I still don’t like the hassle inherent in passkeys, but at least I understand it now.
Oh yeah no problem. The internet is flooded with high level answers that don’t really explain it in any detail.
I wonder what hassle you’re having? Passkeys should be much less hassle than passwords.
The hassle is that I have to have a second device to login with, and I have to keep that device with me and functioning at all times.
Obvious answer is of course my phone, but I’ve had a few situations where I needed to access an account on a new system and didn’t have a 2nd device available.
Unless you lose it or have it stolen.
deleted by creator
Passkeys can’t be lost or stolen in the same way passwords can. They aren’t something you need to learn and are at risk of forgetting, and unlike passwords they never leave your device so they can’t be intercepted, or stolen in a server side data breach. In order for a passkey to be stolen, somebody would need to both steal your phone, and force you at gunpoint to unlock access to the passkey using biometrics.
So they’re much, much harder to lose or “steal”, and the only way they can be stolen, could similarly be used against you to steal your password.
Yes, I think this person is precisely and exactly asking, what if someone steals your phone?
Not so much that they will get access to your data. Even though on secops it’s a given that access to the device is game over. Even if the device is fully encrypted, it’s just a matter of time (even if that time is infinite) to get access.
But, now the user is locked out of their digital life. How do you get back in? There’s nothing you can use to authenticate yourself in with the server if all you had was a passkey. Your data is now inaccessible, great, but utterly lost, not so great. One workaround is to have more than one device with access to all your accounts and never have them in the same physical space or travel with them at the same time. So you don’t lose them both. Or, how most implementers are doing, using all security systems simultaneously. Passkey, passwords, TOTP, 2FA, all at the same time. Such that you can go back into your account if all your devices are compromised.
But, now the user is locked out of their digital life. How do you get back in? There’s nothing you can use to authenticate yourself in with the server if all you had was a passkey.
I’m still not sure what the question is. The same way you would with a password. Using an authenticator app also ties authentication to a single device and yet you don’t seem worried about that. Using “all security systems simultaneously” is not a solution to this problem you’ve suggested which I don’t think really exists. By using all security systems you’re just making your service less secure, not more.
I’m still not sure what the question is.
Using an authenticator app also ties authentication to a single device and yet you don’t seem worried about that.
I didn’t mention it because the comment is not about that (?). But it does worry me. This is why I have 2FA with my authentication/password manager, and do make sure to remember my password to that, because it is the one service remembering all my passwords, TOPTs and passkeys.
By using all security systems you’re just making your service less secure
I agree that it is less secure, but it’s a necessary evil. Furthermore, it’s mandatory. Security and convenience are always at odds. Passkeys theoretically hit a sweet spot of both qualities. But they come with a higher potential for a possible theoretical lockout.
Let’s assume you have an email, you access this via a passkey authenticator that remembers all your passkeys. To access the authenticator you have to provide either a fingerprint on your phone or a password + OTP to your email. This is a system on potential lockout.
If your phone is stolen or destroyed, now you can’t use the phone to access your email, nor login into your email to verify your access to the passkey authenticator. Now you are locked out of your entire digital life. This is not a rare occurrence, it happens everyday. The only reason it’s not catastrophic is because some part of the chain is password only, and the person remembers the password. Or the second factor is on a trusted third party (like cellular carriers reinstating phone numbers via ID check).
Just like welding all doors and windows shut, yes it is more secure, but you also locked yourself out of the house. You want to still be able to enter the house.
Passkeys theoretically hit a sweet spot of both qualities. But they come with a higher potential for a possible theoretical lockout.
But they don’t. I think this is where your confusion is. I think you’re worrying over a problem that doesn’t exist.
Now you are locked out of your entire digital life. This is not a rare occurrence, it happens everyday.
It does not.
If you’re scared of losing both your device and your recovery codes for TOTP, to the point that you store those in your password manager, and you’re happy with that solution, then just store your passkeys in your password manager. Thats literally what this post is about.
And even if you store your passkeys on device for an iPhone for example, they’re stored in your iCloud Keychain which can be recovered if you lose your device. Theres also just nothing about Passkeys that prevent a service from offering an account recovery service.
If you’re already using 2FA, then Passkeys do not pose any additional risk to being “locked out” of your accounts. They actually have less risk usually.
Yes, passkeys are public private keys, so a site only ever sees your public key. Your device does the match with the private key. So in that way, no-one can hack the service site and steal your password. But your private key on your device has to stay very private, and should be synced to another device, because if you lose your private key then essentially you can’t login in. If a site offers a backup “password reset via e-mail” then they have rubbish security anyway.
Everyone should downvote ads type post if you want to keep the community clean.
Can I get an explanation on what exactly passkeys are? I already use bitwarden for passwords, is there any good reason to switch to passkeys if that works for me?
Passkeys are a form of passwordless authentication. You store them in Bitwarden like regular passwords, but when you want to access a site that supports them (e.g. eBay) instead of asking for you password and autofilling or copy pasting it from Bitwarden your Bitwarden pops up and asks you if you want to login and it just happens (if you have multiple passkeys associated with a site you can select which you want to use). That’s it. No password fields which get autofilled and no password in your clipboard (history).
Sounds a lot like SSO no?
It is a similar experience, but you don’t need any infrastructure for it. Everything is handled by your device.
Thanks for the explanation. From the sound of it I’ll probably stick with passwords—i like being able to copy them, cause I’m often signing in to an application, not a website, etc.
That’s a reasonable decision. While passkeys are usually considered much safer than passwords they are not really common. It is mostly the big services (Google, Microsoft, eBay) which have implemented them. Also Bitwarden only supports them on desktop as they are currently working on mobile support. But this will change and as they follow a standard it will be no problem to log into apps with passkeys as the support widens.
Not really, right now as the password resets all undermine passkeys for many sites. One day if/when passwords get replaced then there will be a need, but that is a long way off probably. A good random password along with any 2FA is really good enough for most cases, and Bitwarden already does that very well along with even random e-mail addresses.
Does it beat Bitwarden though? Bitwardan has supported at least 2 services for me using passkeys ,one of which is google.
I might be misunderstanding this,but it doesn’t seem like proton beat anyone to anything.
Edit for info: https://bitwarden.com/passwordless-passkeys/
They’re talking about the fact that Bitwarden doesn’t support passkeys on mobile
Right,yeah,that’s true for mobile indeed.
Sad that these sort of features are paywalled.
Why shouldn’t these features require money?
It’s $10 per YEAR. This is an extremely reasonable price given the importance of the service.
Bitwarden employees need to eat too.
It’s not paywalled. It’s not yet implemented in mobile bitwarden apps. It probably won’t be paywalled once implemented because it’s not paywalled in extension where it’s already implemented
2FA is a paid feature in Bitwarden. That’s the feature we were talking about.
Edit: fuck me for explaining myself
You’re getting downvoted because that, in fact, isn’t the feature we were talking about.
2FA and passkeys are different
I’d be perfectly okay with them just charging for Bitwarden, period. Instead they pretend it’s free but charge premium for all the most effective security features, including 2FA to their own services. Effectively it creates a group of people that use Bitwarden without access to these security features but complacent enough to not seek alternatives that would offer these features at a price acceptable for them (possibly free, like KeepassXC).
Bottom line: security shouldn’t be a premium feature. It should be either available or not at all. Never as a premium within the service.
I disagree.
Simply adopting the use of their free service (or any password manager, sans 2FA) is an upgrade in terms of personal security. That’s moving in the right direction from memorized (and let’s be honest, that means using the same or a small list of similar passwords) passwords everywhere.
The existence of alternatives that include 2FA at no cost works against your point IMO. But that also comes at a cost - Keepass requires that you manage your own sync and backup.
The point of the post was that Proton Pass is beating Bitwarden right now to having passkeys for mobile (Bitwarden has still not released that), and Proton Pass can actually export passkeys which Bitwarden does not do, so they are improving. I would not say though they are better all round than Bitwarden. I pay for both but am still evaluating the rest of Proton Pass vs Bitwarden especially around tweaks in options. But Proton is showing some innovation and momentum, while Bitwarden is slowing a bit. For those already using Proton they will likely find Proton Pass good enough to use right now.
I don’t like passkeys yet because they’re implemented poorly on most platforms, IMHO, because they replace two factors with one. Some don’t let you also turn on two factor auth at all which is dumb, but the ones that do then often only have options that use your device as a factor either through text or email. So if the passkey is your phone and you add text messages as the 2 factor option, that’s still your phone. Or if your passkey is your laptop and you’re logged into your email on the laptop, it’s just one.
Passkeys are 2FA
Could either you or @phoneymouse@lemmy.world explain this for me? If all that’s required to log in using a passkey is access to a single device/provider (e.g. Proton Pass in this case) how does it replace 2FA?
That’s because it’s not 2FA, strictly speaking. The second factor is whatever the device uses to verify you. So, essentially:
You go to a webpage, then go to sign up. Instead of inputting a password, you just input some ID, like a username or email. The device generates a cryptographic handshake with the webpage and your ID. You don’t (can’t, unless you can memorize a string of thousands of letters and numbers and be really good at math with prime numbers) have to remember it.
Now, when you go to login to that page again, the device just remembers and exchanges the keys with the webpage for you. That is NOT 2FA. But, you can configure your device to require another verification (most do). So, when you go to login, then the device asks you to use your fingerprint, or a remembered PIN. Or whatever that confirms that the one handling the device is indeed you before sharing encryption keys with the webpage. This is sorta 2FA, but not really because the webpage is delegating the second factor to the same device actually doing the login. Which might be compromised altogether, but that already happens with most 2FA implementations.
If you go to a second device, and wish to login, then your second device will fallback to other 2FA versions, like sending a OTP to the verified email or phone, or asking you to verify on the one device that is already logged in.
A passkey that’s generated on any given device is tied to that device, and is never sent to the server you’re authenticating to. What’s sent instead is a time based challenge/response that functions similarly to TOTP except that it’s not based on a shared secret like TOTP is. Since the Passkey is both a file, and is tied to the device you generated it on, it satisfied the something you have factor. Then in order to use a Passkey to authenticate, you need to unlock access to it using either biometrics (something you are) or a PIN (something you know).
Now storing your passkeys in a password manager does muddy the process of it a bit. The “something you have” part is no longer a device, but the key file itself, which is still arguably “something you have” but it is to a degree less secure than keeping it tied to a device. But you can think of storing passkeys in a password manager similarly to storing your TOTP in your password manager. It’s a tradeoff.
I know that with 1Password, even if I authenticate to my vault using my master password, when I go to use any particular passkey, it still requires biometrics.
Problem is that if the factor is not authenticated by the server, it doesn’t count. Not saying it’s not helpful, but it’s not part of the consideration when designing the security of the system.
The device can be attacked for an indefinite time and the server knows nothing about that. Or the device can disable that additional security either knowingly or maliciously and the server has no knowledge of that breach. So it’s still a single factor, “something you have” to the perspective of the server when considered security.
I’ve worked with healthcare data for decades and am currently a software architect, so while it’s not my specialty directly, it is something I’ve had to deal with a lot.
I believe passkeys are supposed to replace 2FA and passwords. If you have a passkey, you’re not supposed to need 2FA.
I started using Strongbox on iPhone & Mac for passkey support Bitwarden is still there too, esp for PC, but I may move to an all KeePass setup.
I’m not 100% clear on the pricing. Do I get this for “free” as part of a premium subscription to Proton Mail/Drive/Calendar or is this a separate subscription?
Probably best to see their comparison but free account mainly excludes Integrated 2FA authenticator and only has two vaults, but unlimited logins. I’m on the unlimited account (for VPN and mail) so can’t check for sure.
This is included in the premium subscription
Nice. Thx.
Just an FYI, they’re lying. It’s free for everyone.
The real question is why the fuck is this guy passing for two password managers if not more, especially if he isn’t even using one?
I really really like proton pass, was using Google password manager prior but I primarily use Firefox and Firefox’s password syncing is just bad. Proton pass has been a surprisingly reliable password manager.
It does seem to have innovated quite quickly. I’m still using Bitwarden as I have the paid access to biometrics etc, and it has a nice tweak also to add unique e-mails for every login, etc. But I’m interested to see where Proton Pass will be in another few months, seeing I’m already paying for their service, and maybe I can consolidate my expenses a bit. I actually got drawn into paid Proton by leaving ExpressVPN, which I needed for Netflix, and then found Proton (with one or two others) were the only one’s handling Netflix’s geofencing quite well. Looking at options is always good.
I was considering Proton Unlimited and moving away from separate SimpleLogin and Bitwarden Premium to get my costs down. Has anyone moved from Bitwarden to Proton Pass? How was the experience?
I moved FROM Proton when I started looking into using unique addresses for everything via my own domain.
Fastmail + Bitwarden is way cheaper than Proton + SimpleLogin.
I found myself wondering why Proton, which I was already paying for, required an additional cost to implement masked email addresses via SimpleLogin when they own the damn thing.
Fastmail just has all of that baked in for cheaper. Then Bitwarden can create masked addresses from its interface via API when you create logins.
I liked the look of Fastmail but I read that it doesn’t work offline which seems to be a massive oversight. I also only really need basic mail but their 2GB limit felt way too low for a paid service.
Hm. I guess I’ve never had the need for offline support so I didn’t notice. Though IMAP works so other clients could take care of that.
Why did you compare the lowest tier with Proton Unlimited?
- Proton Unlimited: $120/500GB/15 addresses. Add cost for SimpleLogin to manage masked addresses.
- Fastmail Standard: $50/30GB/600 addresses. Masked addresses built in at no extra cost.
I don’t know your storage requirements but for me, I never went over the 15GB free limit in Gmail after many years of use so I don’t see 30GB ever being a problem.
Edit: After more looking, SimpleLogin may be included with Unlimited? Still… Unlimited is expensive. This may have been what caused me to start looking elsewhere. I had been paying for Proton Mail Plus plan for a few years before I started looking at implementing masked email addresses and got frustrated with the price to use SimpleLogin features which weren’t included in Plus.
I don’t have Unlimited. I pay for Mail Plus. I also pay for SimpleLogin and Bitwarden. By moving to Unlimited I get SimpleLogin included and could ditch Bitwarden.
I don’t see a way to import from SimpleLogin with Fastmail so don’t see it being an option anyway. I really don’t want to manually create 350 aliases.
When I get on my PC I will look again at my options. Thanks for your input.
As a counterpoint, I’m specifically keeping passwords with a separate service out of concern in having a single point of failure for the majority of my online persona. I do pay for proton unlimited but mostly for VPN, simple login, and email.
This did cross my mind yeah. Also by putting all your eggs in one basket you kind of get trapped in that ecosystem. No different to Google / Apple.
Has anyone used pass keys? I have been hesitant to try them out. Using them, do they basically keep you logged in all the time to a given site?
I’ve had them since 1Password beta. They do not change the duration of a session unless the service opts to. In the case of google they ask me to log in more often, presumably because there’s less friction, so why not?
Only for a test, I do not see myself switching to passkeys any time soon, using KeePass is fine in my use case. If there would be some site for which I would need to authenticate every day I would probably create a passkey on device itself (Windows Hello or Google Password manager) since authentication speed increase is undeniable.
Only authentication method changes, there should be no difference after you sign-in, how long sign-in is kept still depends on site owner.
There are various sites to test authentication experience, here’s one where you can test it with dummy account and no registration https://webauthn.io/. It is pretty cool, but you need to create a passkey for every site on all devices to fully utilize their potential.
I use passkeys for some sites, but have been reluctant to go all in until I’m sure all my devices can support them. I’m not always going to have my desktop with me, and likewise my phone’s battery can be flat, etc. I’ve always wanted passkeys to first sync across all my devices, and ideally to be exportable and brought into a different service. Right now you can export your 900+ passwords, and import them into a different service if you want to move. You can’t do that with Apple or Google passkeys.
Passkeys seem like mtls…so much so that I’m not sure what the difference is.
There is a difference but right now as long as one uses a good password with a 2FA it is probably good enough. Too many services with passkeys are still quickly offering password resets via e-mail or text, so they, as sites, are not secure. And unless you can move your passkeys with you, like you can with passwords, you don’t want to get locked into a single device or OS.